by Gordon Duff, VT Sr. Editor, …with New Eastern Outlook, Moscow
Introduction: The story below is a teaser. It might well be a book that could never be published or a feature film, perhaps a great one, that a Harvey Weinstein clone would keep from distribution.
The reason you are reading this is simple, we know it is going to be tried again. The Deep State, and it isn’t “Israel,” certainly not Israel alone, but something far more sinister, something that touches every aspect of your life, every story you read, every email you open, the crackpot ideas your friends espouse, the mysterious collapse of your employer, the endless ripoff calls you receive on your phone, the hive-mind of the Deep State is milking this planet – no, more correctly, bleeding it to death.
We know a new MH17 is planned and that Israel will be the tool to pull it off, their technological genius (with other people’s ideas) and their willingness to do harm, something not unique to them, not hardly. “Moral relativity,” and by that I mean group dynamic psychopathy, abounds.
Between PMCs (Private Military Contractors) and the internet monstrosities of Google and Facebook, engineering false flag terrorism and mass murder is likely to become a real market sector alongside the Dow Jones Industrials.
The evidence behind what is given here would fill terabyte drives, the witnesses not yet silenced abound as well. MH17 opened a door that the US opened when it shot down Iran Air flight 655 on July 3, 1988, a monstrous war crime and then gave the captain of the USS Vinccennes the Navy Cross for murdering 290 civilians, mostly women and children.

Brazen, that’s the only word that comes to mind. So when the US passes out W54 nukes to Israel to drop on Syria and Yemen, new secretly redesigned 1970’s mini-nukes that can fit into the bomb bay of the otherwise useless F35, a story we confirmed at the highest levels with multiple sources, the decades old lie machine had no trouble dealing with it.
MH17 was just another one with “Charlie Hebdo” and the mysterious dissolution of Building 7 on 9/11 using more mini-nukes, the 9000 first responders with radiation poisoning (multiple myeloma), oh, you didn’t know? “Toxic soup?” Heinz or Campells? Chicken noodle, tomato possible? Perhaps ionizing radiation from nuclear weapons.

MH17 was simple, it was nothing for a pair of Ukrainian SU27s to down an airliner, playing the same game Israel now uses all the time in Syria, certainly before Christmas 2018 and again in September when a Russian IL20 was lost with all aboard.

Addendum I
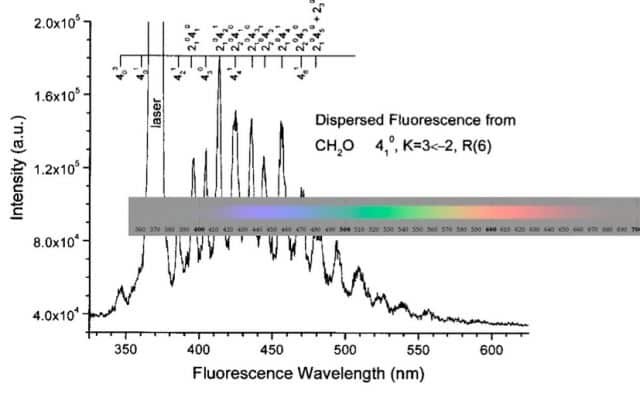
Let’s take a second to talk about “proofs.” For our story here, which is confirmed with mountains of evidence, to be fake, one thing would have to be true. What is said is that radar spoofing is impossible. We refer to Addendum I, for a technical explanation. We also might do some graphics for you, perhaps I might sell you the equipment in case you want to shoot down an airliner yourself, anyone can do it it seems.

How it looks on the ground:
 But you need one of these as well, which was driven off the back of a US built C130 with a “Star of David” on the tail. Americans at least use unmarked planes for ferrying ISIS around.
But you need one of these as well, which was driven off the back of a US built C130 with a “Star of David” on the tail. Americans at least use unmarked planes for ferrying ISIS around.

Hell, let’s look inside a radar spoofing box:

Or perhaps we can see what kind of things they can do:

Then again, our story, which was brought to us by a Canadian group that tracked the flights out of Azerbaijan that aided in the intercept, requires some proof that Israel uses F15s for long range command and control. That was denied also but took 15 seconds to disprove:

We can prove it all, in depth, with high certainty, as we can with a dozen or more false flag “terror” events. Now, on to New Eastern Outlook:
– First published … December 31, 2018 –
Moscow: Is Russia targeted by a thousand-year-old criminal conspiracy that, so very long ago, built a system of central banks and set monarch against monarch, century after century? Is this the Deep State Trump tells of, a network of “oligarch,” central banks and industrial cabals?
Do they now stage terror attacks, down airliners and own the world’s press?
On Christmas Day, 2018, Israeli planes attacked Syria by hiding behind two civilian airliners, one landing in Damascus. The Lebanese government complained vigorously about the violation of its airspace and the insanity of the Israeli action, only days after Israeli Prime Minister Benjamin Netanyahu received a “no confidence” vote that may well remove him from office after charges of broad corruption had been filed against him.
A similar attack was waged on Syrian and Russian forces on September 19, 2018 when Israeli planes following a Russian IL20 military aircraft coming in for a landing, used the Israeli “human shield” ploy leading to the deaths of 15.
Evidence from sources in Kiev now indicate that the downing of MH17 in 2014 involved Israeli teams operating in Kiev, Israeli pilots flying from bases in Ukraine and Azerbaijan and the use of MH17 as a “human shield.”
This time, however, there were no ground targets worthy of attack but rather the incident itself, much like the White Helmets’ fake gas attacks, staged to manipulate opinion and draw NATO and the US into the conflict.
The scenarios go as follows:
- Israeli pilots flying Ukrainian aircraft, most likely SU27 aircraft with Israeli built “radar spoofing” to make them seem like SU25 ground attack craft, shadowed the Malaysian Airlines flight.
- The Mossad had placed air controllers in Kiev that redirected the civilian airliner over a specific spot which should have been a “no fly zone” because of the history of air combat over that area.
- Bolstering the capability was an Israeli F15 with powerful radar and a two-man crew, flying out of Azerbaijan. Israel had maintained a capability there since 2010, as reported by defecting Azeri officers who told Iranian officials of the Israeli air presence there, placed there to attack Iran.
At this point, based on the level of this accusation, it is necessary to provide documentation, from the Reuters News Agency:
By Thomas Grove (Reuters) – Israel’s ‘go-it-alone’ option to attack Iran’s nuclear sites has set the Middle East on edge and unsettled its main ally at the height of a U.S. presidential election campaign.
Prime Minister Benjamin Netanyahu exudes impatience, saying Tehran is barely a year from a ‘red line’ for atomic capacity. Many fellow Israelis, however, fear a unilateral strike, lacking U.S. forces, would fail against such a large and distant enemy.
But what if, even without Washington, Israel were not alone?
Azerbaijan, the oil-rich ex-Soviet republic on Iran’s far northern border, has, say local sources with knowledge of its military policy, explored with Israel how Azeri air bases and spy drones might help Israeli jets pull off a long-range attack.
That is a far cry from the massive firepower and diplomatic cover that Netanyahu wants from Washington. But, by addressing key weaknesses in any Israeli war plan – notably on refueling, reconnaissance and rescuing crews – such an alliance might tilt Israeli thinking on the feasibility of acting without U.S. help.
It could also have violent side-effects more widely and many doubt Azeri President Ilham Aliyev would risk harming the energy industry on which his wealth depends, or provoking Islamists who dream of toppling his dynasty, in pursuit of favor from Israel.
There is much more behind this story, including complicity by the Georgian government in transiting bombs offloaded at the Georgian Black Sea port of Poti in June 2010, delivered by the USS Grapple, a ship offloaded by personnel who immediately reported the cargo and its destination to VT Bureau Chief Jeffrey Silverman.
We return to the narrative: The plan, we are told by our sources in Kiev, was to see to it that MH17 was downed, either by a missile placed in the altered flight path of the Kiev regime working with Israeli intelligence or, if that failed, shoot down the plane using the fighters shadowing the plane.
On 21 March 2018, the Ukrainian pilot, Vladyslav Voloshyn, who was wrongly accused of piloting a “low level” SU25, that our sources tell us was really SU27s piloted by Israeli Air Force pilots “killed himself.” Our sources say he was murdered. From the UK Independent:
A Ukrainian pilot falsely accused by Russia of shooting down Malaysian Airlines flight MH17 in 2014 has reportedly killed himself.
Captain Vladyslav Voloshyn, who piloted a low-flying Su-25 attack jet, shot himself at home in Mykolaiv, his hometown in southern Ukraine, local media said.
Russian officials and media had accused Mr. Voloshyn of flying the jet which shot down the Boeing 777 passenger plane, killing all 298 people on board.
However, a two-year Dutch investigation concluded the plane had been destroyed by a Russian Buk missile.
Below is language from a confidential legal communication between a Washington law firm and the Prime Minister of Malaysia regarding this issue:
“Prime Minister Dato’ Sri Mohd Najib bin Tun Haji Abdul Razak
Prime Minister’s Office of Malaysia
Main Block, Perdana Putra Building Federal Government Administrative Centre 62502 Putrajaya, Malaysia
9 September 2014
Re: Malaysia, Khazanah and Malaysia Airlines
Dear Prime Minister Tun Najib:
Thank you for considering our proposal to represent Malaysia and assist you in developing domestic and international coalitions on legal and other issues related to Malaysia Airlines.
We appreciate and thank you for your superb diplomacy in resolving the international issues that have defied lesser leaders. We may enable you to achieve even greater success.
We offer to represent Malaysia in the following areas in which we may be of significant value to Malaysia, Khazanah, your national airlines and you:
Legal Counsel on issues linked to MH 17, MH370, MAS and Malaysia Airlines (e.g., restructuring, rebranding, union issues, criminal and civil court cases, etc.); …
If you would like International Criminal Court jurisdiction for MH17 crimes, then we would counsel and assist you in obtaining such jurisdiction and act on your behalf in the United Nations, Ukraine, Russia, China, France, United Kingdom, and the United States of America.
Our attorneys are ready, willing and able to take the lead in obtaining justice for Malaysian and other families and your airlines due to the downing of MH17. We are willing to manage complex multinational litigation required to achieve justice for victim families and your airlines — against Ukraine, rebel assailants, Russia, USA, insurance companies and/or others.”
After private consultations, in which I was personally involved, the Malaysian Prime Minister advised that he had been threatened and would not be “permitted” to see justice. The threats were from sources attributable to our definition of “Deep State.” None of this information has been made public prior to this.
New sources have come forward that places the crash of Malaysian Airlines flight MH17 that went down over pro-Russian regions of Eastern Ukraine on 17 July 2014. If correct, and procedures for rating intelligence sources would rate this information as “actionable” with “high confidence,” it puts a new light on events over the last few months.
Intelligence is, as is now portrayed in media as well, a mosaic but seldom involves “dot connecting” as is done on conspiracy blogs or, as has been revealed by President Trump, on the mainstream media as well.
Simply put, Russia is a targeted nation, its vast landmass and endless natural resources, have put the “black spot” on Moscow for hundreds of years. What Hitler and Napoleon failed at, didn’t end. Others have been fighting a political, a propaganda, an economic war on Russia all along.
“Russiagate” is a part of that war, the Skripal incident as well, along with accusations of Russian complicity in chemical weapon attacks in Syria.
Past this, there is strong evidence Russia is targeted by a biological warfare operation run by the United States out of Tbilisi, Georgia, one that may well have recently released, perhaps accidentally, a deadly weaponized influenza pathogen on Georgia itself. These “accidents” have happened before as has a strange and inexplicable Swine Flu epidemic that jumps thousands of miles with no plausible vector.
Today we begin pointing fingers. In order to do so, we need to put a rough definition on what or who the Deep State really is. The term, coined by Trump but in various forms an expression of an “unseen actor” behind super-governmental manipulation that historians only discuss at great personal risk, has a history, real people, real names, a trail through history for not just generations but centuries.
Using the term “international bankers” or “robber barons” is gross understatement. We have a clear history of banking families expelled from England in 1290 by Edward I, expelled from Spain in 1492, and much of their history since.
Were one to look at the recent economic collapse in the US at the hands of the Federal Reserve “Bank,” the same cast of characters, the real Deep State, comes into focus. We can start with Spain prior to 1492, where the Palenzuela banking family was bleeding the nation through high interest loans. Spain’s gold laden empire in the New World was a century away.
The enemy, the Palenzuela banking cartel, who fled to Venice in 1492 taking on the name “del Banco,” or “of the bank,” dropping their name and their criminal history. From there, they moved to the town of Warburg in Germany and changed their name to “Warburg.” If this sounds familiar, it was Paul Warburg who authored the Federal Reserve Act in 1913 and was first Chairman of the Federal Reserve.
First America got an illegal central bank, one outlawed in her constitution and only a few short years later, America found herself at war in Europe. Coincidence?
There are more names, the Astors, really the Astorgas expelled from Spain, and then there were the Cabots, or rather the Cabotas, also expelled from Spain. These were the great American fortunes built on slavery and the opium trade, once run from China but now from Afghanistan by the CIA, still under control of the same families.
This is the deep state and there are more names, some you will know, some you won’t and new names, the “oligarchs” and “kingpins” that sit in the shadows and pull the strings.
Added to the mix are the great manipulators, Google Corporation, Facebook and an unseen army of “Silicon Valley warriors” who have established a stranglehold on politics, commerce, culture and even “human awareness” around the world. They represent a Deep State intelligence, a “world consciousness” and that consciousness is pathologically insane and criminal in nature.
Though a thousand years old or more, they change, they adapt, and their patterns are visible. They are ISIS, they are al Qaeda, they are the CIA and MI6, they buy governments, they wage wars, chaos is their tool and humanity is fodder to them.
Anything not under total control is a threat.
Addendum I
By Gene “Chip” Tatum for VT
[ Editor’s note: I asked Chip to do this piece based on his background with the technologies and how vital it is for the public to know that all information about plane locations, altitudes, speed or even plane type have been faked though EW (Electronic Warfare) modules for years. Thus, the radar tracking from 9/11…faked…the SU25s tracking MH17….faked as well, wrong altitude, wrong planes, maybe not even Ukrainian or Russian at all. An Israeli F15 taking off from Azerbaijan was “there.” Did it magically turn into two SU 25′s? We can prove it could have. What Chip proves is that efforts to sell government conspiracy theories based on faked radar is going to have to come to an end. We are busting them now.g ]
In 2010, Israeli fighters bombed a suspected nuclear materials site in Syria. Here’s the million dollar question: How did they do it without tipping off Syria’s Russian-bought air defense radar? Israel hacked the network.
So lets consider what means could have been used and even more, how technology has advanced in the last four years.
DARPA and the U.S. Air Force are prime users and developers of radar systems, using them for early warning during the Cold War, when the Air Force had both airborne and ground based radar systems deployed around the world to guard against and detect Soviet aircraft. Radars were and continue to be one of the most important pieces of equipment on modern aircraft. The faster and farther away an adversary can be identified and accurately tracked helps to give the pilot an edge that can be vital during combat. Electronic warfare techniques (EW and ECM) and technology have been in use since World War II and go hand in glove with radar systems. These technologies are often used to jam, counter jam, spoof, or confuse enemy radar operators and weapon systems, allowing the aircraft to accomplish their mission.
But what exactly is Radar? And how does it work? And better yet, how can you Spoof or Fool it?
The basic idea behind radar is very simple: a signal is transmitted, it bounces off an object and it is later received by some type of receiver. This is like the type of thing that happens when sound echo’s off a wall. (Check out the image on the left) However radars don’t use sound as a signal. Instead they use certain kinds of electromagnetic waves called radio waves and microwaves. This is where the name RADAR comes from (RAdio Detection And Ranging). Sound is used as a signal to detect objects in devices called SONAR (SOund NAvigation Ranging). Another type of signal used that is relatively new is laser light that is used in devices called LIDAR (you guessed it…LIght Detection And Ranging).
Radio waves and microwaves are two types of electromagnetic waves. Electromagnetic waves, which I will call EM waves, like all waves, transport energy but can do so through a vacuum. Sound waves and ocean waves require matter to transport energy, but EM waves can do so without the presence of matter. Because of this, satellites can use radars to work on projects outside of the Earth’s atmosphere and on other planets. Another useful thing about EM waves is that they travel at a constant speed through a vacuum called the speed of light abbreviated by the letter “c” (299,792,458 meters per second). This is very useful to know to when doing ranging calculations. Once the radar receives the returned signal, it calculates useful information from it such as the time taken for it to be received, the strength of the returned signal, or the change in frequency of the signal. This information is then translated to reveal useful data: an image, a position or the velocity of your target.
When an EM wave hits a surface, it gets partly reflected away from the surface and refracted into the surface. The amount of reflection and refraction depends on the properties of the surface and the properties of the matter which the wave was originally traveling through. This is what happens to radar signals when they hit objects. If a radar signal hits a surface that is perfectly flat, then the signal gets reflected in a single direction (the same is true for refraction). If the signal hits a surface that is not perfectly flat (like all surfaces on Earth) then it gets reflected in all directions. Only a very small fraction of the original signal is transmitted back in the direction of the receiver. This small fraction is what is known as backscatter. The typical power of a transmitted signal is around 1 kilo-watt and the typical power of the backscatter can be around 10 watts.
To determine the range of a distant object that reflected a radar signal, the receiver must record the time when the signal was received and compare it to when that signal was transmitted. This time is the time taken for the radio wave to propagate to the object and back to the antenna. Since all EM waves travel at the speed of light in a vacuum, 299,792,458 meters per second (Air is not quite a vacuum but EM waves still travel through it at approximately this speed) it is very easy to determine how far away the object is (just multiply the speed of light by the time for the signal to get received).
Another thing the radar does when it receives a signal is determine how strong it is. For ground penetrating radars the strength of the signal can tell how much the beds under the surface have different properties. A higher received power indicates a larger difference between neighboring beds.
Radars are being used to measure different parameters
1. Range Using Pulse Delay
2. Velocity From Doppler Frequency Shift
3. Angular Direction Using Antenna Pointing
4. Target Size From magnitude of reflected energy
5. Target Shape Analyzing reflected signal as a function of direction
6. Moving Parts Analyzing modulation of the reflected signal
Cost and complexity of radar is dependent upon the number of functions it performs. Radars are used for various applications like surveillance, imaging, remote sensing, altitude measurement, etc.
Blip enhancement is an electronic warfare technique used to fool radar. When the radar transmits a burst of energy, some of that energy is reflected off a target and is received back at the radar and processed to determine range and angle. The reflected target energy is called skin return, and the amount of energy returning to the originating radar is directly proportional to the cross-sectional area of the target.
Basic radars present the target information on a display and displayed targets are referred to as blips. Based on the relative size of the blips on the display, a radar operator could determine large targets from small targets. When a blip enhancing technique is used, small targets returns are augmented to look like large targets.
Electronic Counter Measures (ECM) is practiced by nearly all modern military units—land, sea or air. Aircraft, however, are the primary weapons in the ECM battle because they can “see” a larger patch of earth than a sea or land-based unit. When employed effectively, ECM can keep aircraft from being tracked by search radars, or targeted by surface-to-air missiles or air-to-air missiles. An aircraft ECM can take the form of an attachable underwing pod or could be embedded in the airframe. Fighter planes using a conventional electronically scanned antenna mount dedicated jamming pods instead or, in the case of the US, German, and Italian air forces, may rely on electronic warfare aircraft to carry them.
Today, Satellites may play a major role in ECM.
But lets get back to the 2010 Raid on Syria by Israel. The system used for the raid is called Suter.
U.S. aerospace industry and retired military officials indicated today that a technology like the U.S.-developed “Suter” airborne network attack system developed by BAE Systems and integrated into U.S. unmanned aircraft by L-3 Communications was used by the Israelis. The system has been used operationally in Iraq and Afghanistan.
The technology allows users to invade communications networks, see what enemy sensors see, and even take over as systems administrator so sensors can be manipulated into positions so that approaching aircraft can’t be seen or seen in false positions ans false sizes. The process involves locating enemy emitters with great precision and then directing data streams into them that can include false targets and misleading messages algorithms that allow a number of activities including control.
BAE and the Suter system developed and used in 2010 have made major advances in abilities. Not only can the system Spoof location, bearing, heading, and target size, but it can also project misleading information on aircraft in the vicinity.
For example, let’s say for sake of discussion that a fighter jet was flying missions in the Ukraine against Russian Separatists. Separatists missile defense systems would readily detect such flights, identify it as a foe via the ground radar systems, and lock on in preparation for launch. The Sutor software, however, could forward project data showing their aircraft in another location. The launched missile would then seek a hard target after launch seeking any hard target in the area. If that happened to be a commercial airliner, the missile would automatically lock on and destroy that target. If it could not acquire a target, it would search until fuel supply runs out and fall to earth.
Today’s electronic battlefield is more complex and deadly than ever-particularly when it comes to electronic surveillance and electronic warfare.
Gordon Duff is a Marine combat veteran of the Vietnam War that has worked on veterans and POW issues for decades and consulted with governments challenged by security issues. He’s a senior editor and chairman of the board of VT, especially for the online magazine “New Eastern Outlook.”
https://journal-neo.org/2018/12/31/the-deep-state-s-secret-war-on-russia/
Related articles:
MH17 Was Really MH370


Gordon Duff posted articles on VT from 2008 to 2022. He is a Marine combat veteran of the Vietnam War. A disabled veteran, he worked on veterans and POW issues for decades.
Gordon is an accredited diplomat and is generally accepted as one of the top global intelligence specialists. He manages the world’s largest private intelligence organization and regularly consults with governments challenged by security issues.
Duff has traveled extensively, is published around the world, and is a regular guest on TV and radio in more than “several” countries. He is also a trained chef, wine enthusiast, avid motorcyclist, and gunsmith specializing in historical weapons and restoration. Business experience and interests are in energy and defense technology.
ATTENTION READERS
We See The World From All Sides and Want YOU To Be Fully InformedIn fact, intentional disinformation is a disgraceful scourge in media today. So to assuage any possible errant incorrect information posted herein, we strongly encourage you to seek corroboration from other non-VT sources before forming an educated opinion.
About VT - Policies & Disclosures - Comment Policy





In Europe airplanes disappeared twice from the Radar than:
http://www.focus.de/panorama/welt/mysterioese-stoerung-ueber-europa-13-flugzeuge-verschwinden-minutenlang-spurlos-vom-radar_id_3917938.html
http://deutsche-wirtschafts-nachrichten.de/2014/06/14/mysterioes-dutzende-flugzeuge-in-europa-verschwanden-ploetzlich-vom-radar/
http://www.spiegel.de/politik/deutschland/flugsicherung-radarstoerungen-durch-nato-manoever-a-981575.html
interesting is the Date, when the last news was published, is that still a coincidence or already a leak? Gebauer made it from ‘Bild’ to Chefreporter of ‘Spiegel online’.
Here’s a pretty good read. It goes into more about the photo that was taken when the original MH370 disappeared. The guys name is Phillip Wood. He was an employee for IBM.
http://www.cabaltimes.com/2014/03/12/ma370-redirected-to-diego-garcia/
Here we go:
https://www.liveleak.com/view?i=fbf_1429163375
I saw it. It’s not fake. I saw the bloated bodies and the guy(lady) walking around the crime scene. It’s obvious this is the missing plane they flew into Diego Garcia. There is also a “picture” a guy took that was on the original plane that just “disappeared”. The guy took a picture after they landed and sent it. It was totally black but you could see from the coordinates it was sent from Diego Garcia.
All the passports were brand new at the wreckage site, some even had the punch taken out of them, expired. I saw it just a couple of months ago. I wish I would have saved the URL. You did have to see it in “the way back machine”. Many of these things on the web are like this now.
these were fake stories as were those that said the bodies were frozen. Imagine FBI agents at NewTown speaking Hebrew for the reporters following them.
Not so secret, everyday I hear from my father, how evil Russia is… Just watch television.
Dad doesn’t watch Fox, just the regular WMAR Baltimore.
Isn’t Vladimir Putin a very patient man? Suppose he became frustrated with the many criminal activities of Israel in Syria and ordered the Russian Military to destroy every military installation in Israel and in the U.S. as well? While this response may have started WWIII it isn’t clear there would be a response from either side since the U.S. Military is busy engaged in criminal activities according to the Steele article and all installations in Israel would have been turned into ashes along with much of the country due to collateral damage. How about the paper tiger NATO? Wouldn’t Putin have had every legal and moral right to take such an action against the two criminal gangster nations on the planet, and isn’t it likely he might have won? The U.S. has not been in a real shooting war since WWII. How do we know anything would work especially with totally corrupt four star generals in charge? How did they do on 9/11/01 “defending” America?
Has there ever been any evidence or intel put forth that shows MH-17 was, in fact, MH-370, after hijacking and murder of the MH-370 passengers?
So Voloshyn has been suicided. Sounds much like the Ćilipi airport navigation control officer Jerkuić “suicide” after Ron Brown’s plane crashed near Dubrovnik, phone calls etc. There is some nasty military intelligence world out there, reporting to us through media from Agatha Christie dimension.
Comments are closed.